
Hi guys, I’m writing my first blog post related to security testing using one of the most popular and open-source tool ZAP. Before that let me brief you about what is security testing and its importance.
1. Overview
Software security testing is the process of assessing and testing a system to discover security risks and vulnerabilities of the system and its data. There is no universal terminology but for our purposes, we define assessments as the analysis and discovery of vulnerabilities without attempting to actually exploit those vulnerabilities. We define testing as the discovery and attempted exploitation of vulnerabilities.
2. Types of Security Testing
Security testing is often broken out, somewhat arbitrarily, according to either the type of vulnerability being tested or the type of testing being done. A common breakout is:
• Vulnerability Assessment — The system is scanned and analyzed for security issues.
• Penetration Testing — The system undergoes analysis and attack from simulated malicious attackers.
• Runtime Testing — The system undergoes analysis and security testing from an end-user.
• Code Review — The system code undergoes a detailed review and analysis looking specifically for security vulnerabilities.
3. Detailed Explanation about Penetration Testing

Penetration Testing (pentesting) is carried out as if the tester was a malicious external attacker with a goal of breaking into the system and either stealing data or carrying out some sort of denial-of-service attack.
Pentesting has the advantage of being more accurate because it has fewer false positives (results that report a vulnerability that isn’t actually present), but can be time-consuming to run.
Pentesting is also used to test defense mechanisms, verify response plans, and confirm security policy adherence.
Automated pentesting is an important part of continuous integration validation. It helps to uncover new vulnerabilities as well as regressions for previous vulnerabilities in an environment which quickly changes, and for which the development may be highly collaborative and distributed.
4. Process and Goals of Pentesting
Both manual and automated pentesting are used, often in conjunction, to test everything from servers, to networks, to devices, to endpoints. This document focuses on the web application or website pentesting.
Pentesting usually follows these stages:
· Explore — The tester attempts to learn about the system being tested. This includes trying to determine what software is in use, what endpoints exist, what patches are installed, etc. It also includes searching the site for hidden content, known vulnerabilities, and other indications of weakness.
· Attack — The tester attempts to exploit the known or suspected vulnerabilities to prove they exist.
· Report — The tester reports back the results of their testing, including the vulnerabilities, how they exploited them and how difficult the exploits were, and the severity of the exploitation.
The ultimate goal of pentesting is to search for vulnerabilities so that these vulnerabilities can be addressed. It can also verify that a system is not vulnerable to a known class or specific defect; or, in the case of vulnerabilities that have been reported as fixed, verify that the system is no longer vulnerable to that defect.
5. Key Advantages of Security Testing
· Secure website from hackers.
· Prevent information stealing.
· Prevent monitory loss.
· Identify and resolve system vulnerabilities
· Gain valuable insights into your digital systems
· Establish trust with your clientele
6. Introducing ZAP
Zed Attack Proxy (ZAP) is a free, open-source penetration testing tool being maintained under the umbrella of the Open Web Application Security Project (OWASP). ZAP is designed specifically for testing web applications and is both flexible and extensible.
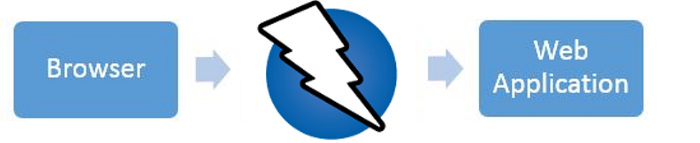
At its core, ZAP is what is known as a “man-in-the-middle proxy.” It stands between the tester’s browser and the web application so that it can intercept and inspect messages sent between browser and web application, modify the contents if needed, and then forward those packets on to the destination. It can be used as a stand-alone application, and as a daemon process.
If there is another network proxy already in use, as in many corporate environments, ZAP can be configured to connect to that proxy.

ZAP provides functionality for a range of skill levels — from developers, to testers new to security testing, to security testing specialists. ZAP has versions for each major OS and Docker, so you are not tied to a single OS. Additional functionality is freely available from a variety of add-ons in the ZAP Marketplace, accessible from within the ZAP client.
Let’s discuss more about OWASP installation and test execution in PART-II
Author: Brinda Giridharan

